by Michael Reinhart | Jul 25, 2021 | Personal
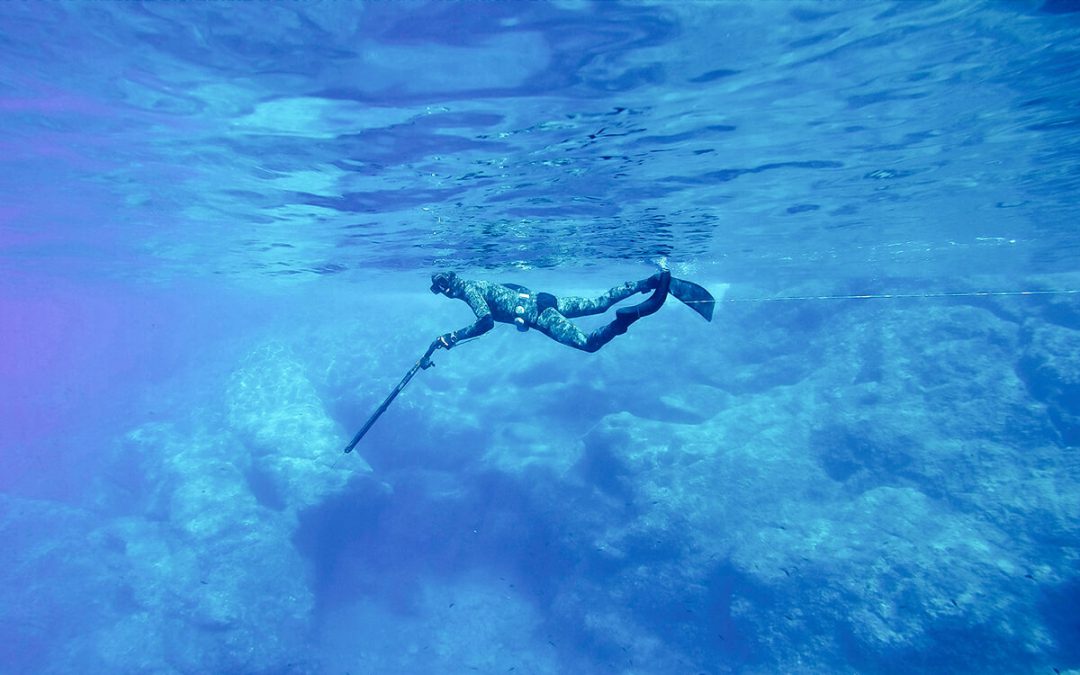
With apologies to Erika Lougheed (I’ll take down if asked), below the embedded Tik Tok video is my transcription of same. Eloquently stated, this is why some of us either can’t get ahead, or almost kill ourselves trying to get there. This is not limited to Ontario. The same conditions exist in Alberta, but the Walmarts and Westons are big oil and gas companies. I grew up here watching boys drop out of school to work in the oil patch, only to suffer when there’s an economic downturn. They start out making an obscene amount of money, but after they become men, because they lack some education and realistic life experience, often spending way beyond their means on big houses, trucks, and toys, they can’t weather the storms of recession. We must invest in people, and reduce wealth inequality.
Don’t let Jason Kenny fool you. He is Boss Hog North of the border.
Citation: Erika Lougheed – @erikalougheed
East Ferris municipal Councillor. ONDP candidate for Nipissing. Potter Artist. Nostalgic for the 90s. (she/her/elle)
Just going for a walk, doing some thinking about the thousand dollar a burger fund raisers, and governing to satisfy government lobbyists and insiders, ultimately promoting wealth inequality by insulating profits for the rich and reducing spending power for everybody else. Our economies exist because of people’s ability to spend. Conservatives reduce people’s spending power when they shape decisions based on the needs of the wealthy. The result is that more of us become poor, and can’t afford to do much. When people are pushed to the brink, conservatives do very little for people in need. They defund our social safety net, and find reasons to blame others, mostly the poor for not working hard enough. And no amount of touring local small businesses can roll back the poor covid response where conservatives demonstrated their true allegiance to the Walmarts and Westons to the world. And people without the ability to spend are not able to shop at our local or eat out at our local restaurants because they can’t. We need to elect a government that will work to reduce wealth inequality and invest in people, not insider profits, for a healthy economy. And that my friends is why conservatives are very bad for business.
by Michael Reinhart | Jul 18, 2021 | Personal
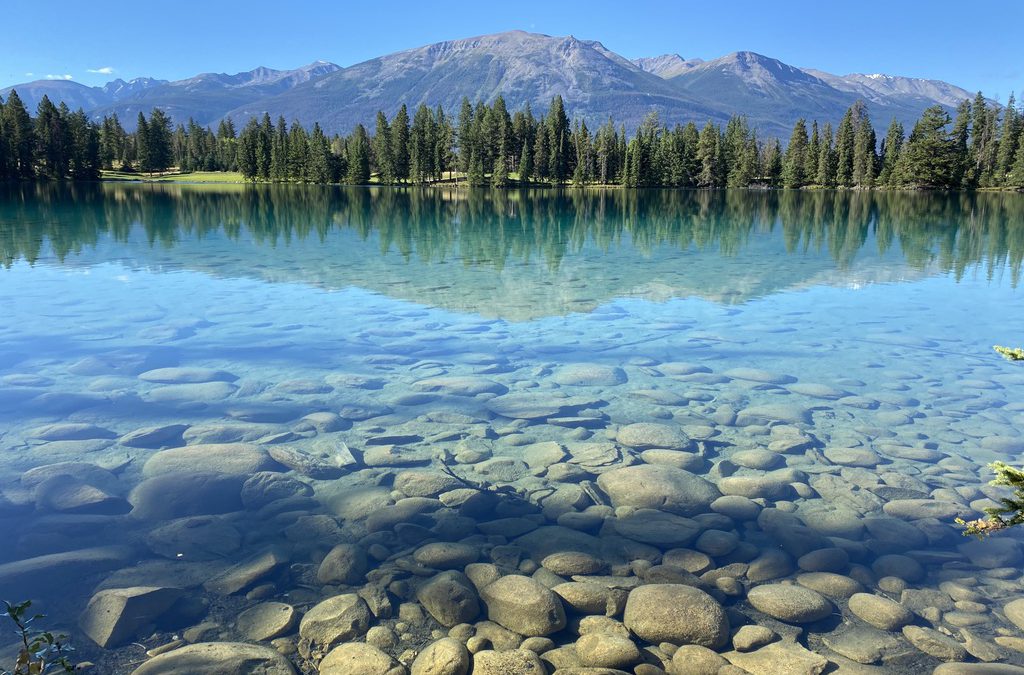
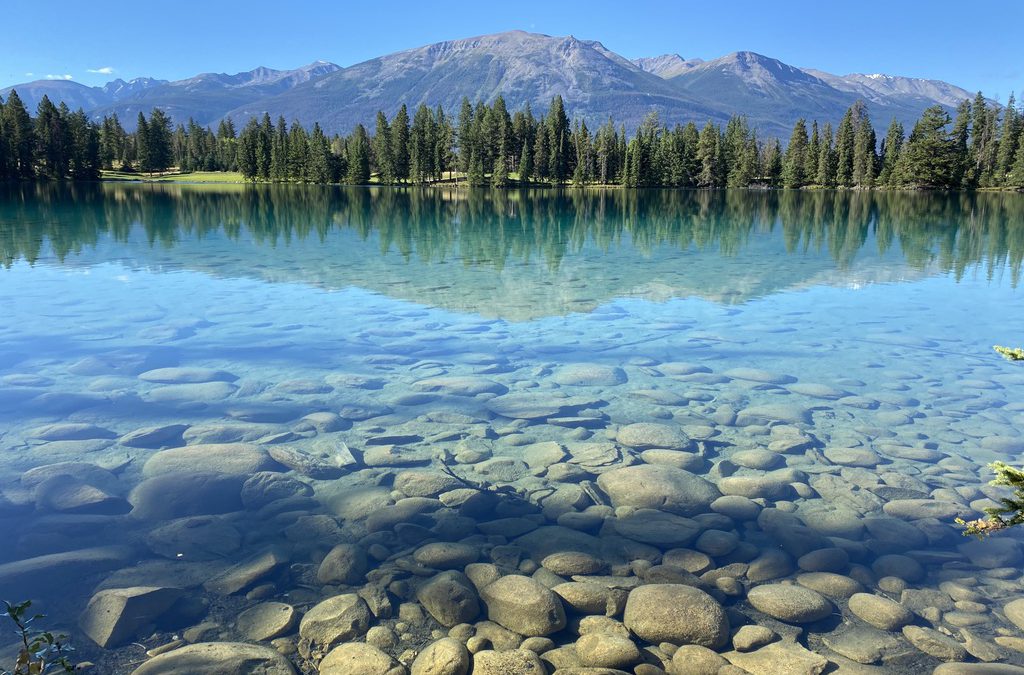
Dear neighbour and friend,
You may be newer to this place than me. You may have been here long before me. You may worship, or not. You may wear clothing that’s different from mine. Maybe you listen to music that I can’t make sense of. Or perhaps you prefer to drive slower than me. Or eat things I can’t identify.
I may not know much about you, or what you’ve been through. I might have traditions that seem peculiar to you. We may sound different from each other. Our fortunes, or misfortunes, may have been very different. Your life may have been ordinary, or a genuine odyssey. Your sheer existence may be a miracle, or something more humble.
We are in this together. I will look out for you. Our combined experiences can make us better together. We share not only a desire for happiness, but also DNA.
Will you look out for me? Can we share our Canadian experience? Can we build a future of joy, compassion, and kindness together?
by Michael Reinhart | Jul 17, 2021 | Personal
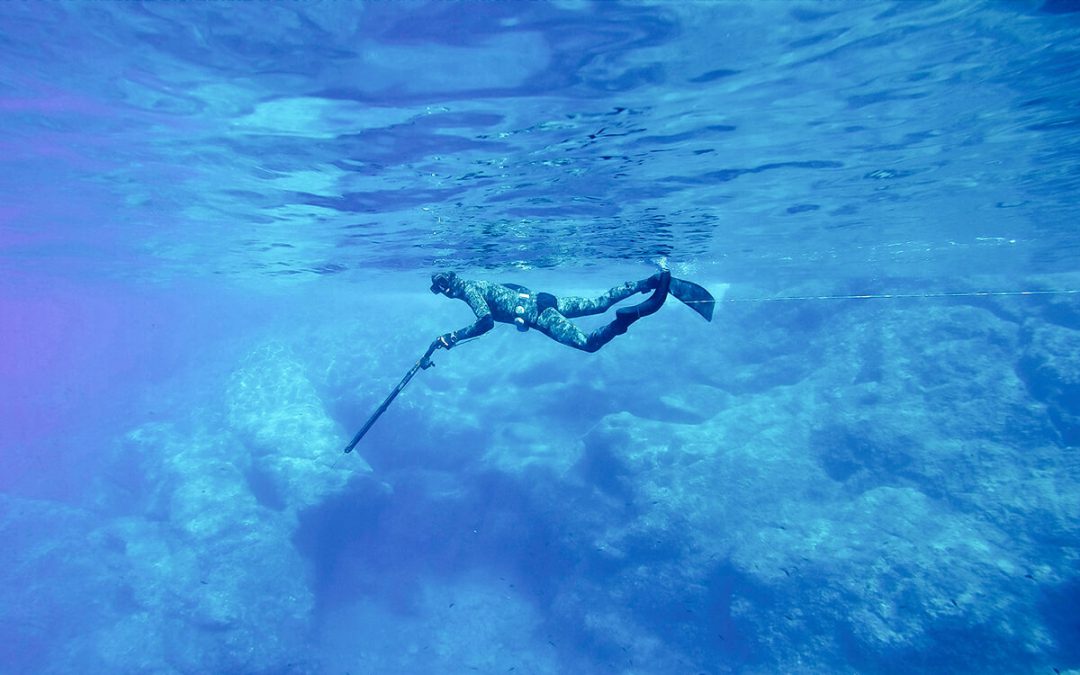
We’re seeing an evolution of this precisely targeted kind of phishing attack. They’re getting increasingly sophisticated, and increasingly malicious. In one client’s case, they not only successfully got his Office 365 password, but they immediately logged in with them, deleted all their files from OneDrive, and set up an automation on the account to delete all incoming email.
It’s becoming common practice to train employees in techniques to spot phishing attacks, and you can proactively engage us to perform vulnerability assessments and provide proven recommendations to mitigate these risks.
Have you thought carefully about your level of risk tolerance? What would happen if all your files disappeared this afternoon? Are you prepared? We can help.
by Michael Reinhart | Jan 30, 2021 | Highlights
Many of our clients have asked if we build web sites. In fact, that’s where Above Studio 1 began.
Back when the internet began, when Webmaster was a job title, and we all had to figure out what a TCP/IP stack was, I started a web hosting company called Webstead, which I later sold. Things have come a long way since then– frameworks, WordPress, Shopify, and other revolutionary standards-based tools ease the complexity of building great looking web sites, and we leverage these.
Our design aesthetic is minimalistic, and we prefer a great user experience over flashy decoration. Whether it’s just a basic presence on the web you need, or something more advanced that integrates with your other systems for automation, contact us to talk more– we’d love to hear from you.
by Michael Reinhart | Oct 26, 2020 | Business, Highlights, Small Business
A recent Wipro study indicated 59% of employees would choose a Mac if given a choice, though only 32% are already using one. Whether it’s a fleet of iPads, iPhones, or Macs, we can deploy and manage all of those devices, including software, without touching them. They can be delivered directly to staff, ready to go almost as if by magic.
The pandemic means tens of millions of employees are now working from home, many for the first time. Even reluctant enterprises have been forced to support this, and in most cases have found that remote workers still get work done.
What about new employee onboarding?
One of the challenges raised by some enterprises concerns the problem of bringing new employees aboard at a time of social distancing. In this regard, Hager shared his own company’s experience recruiting and onboarding new staff:
“We sent everybody home on March 12,” he said. “Since that time, we have fully remotely onboarded over 70 employees and we brought on over 30 summer interns. We fulfilled our internships to over 30 students this summer, and they never came in to work. They were actually very productive all summer long, did a terrific job for us.”
https://www.computerworld.com/article/3573387/how-apple-is-being-deployed-across-the-covid-19-enterprise.html
Contact us to find out how we can make this journey easier.